- Ledger’s Donjon team exploited MediaTek phones, recovering PINs and crypto wallet seed phrases
- Attackers can extract root cryptographic keys from switched-off Android devices via USB
- Trustonic’s Trusted Execution Environment fails to prevent attacks on one-quarter of Android devices
Ledger’s white-hat hacking team, the Donjon, discovered a vulnerability in MediaTek-powered Android smartphones which allows attackers to access sensitive data in under a minute.
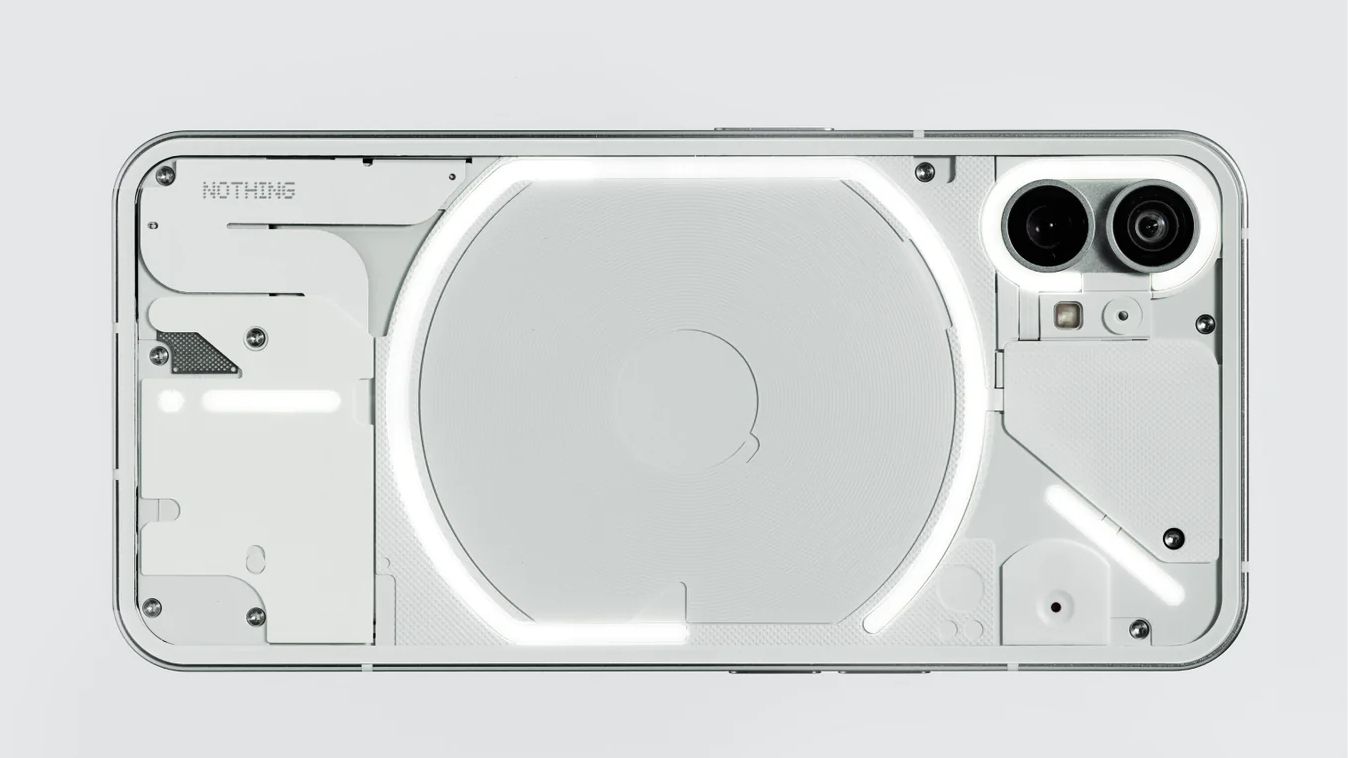
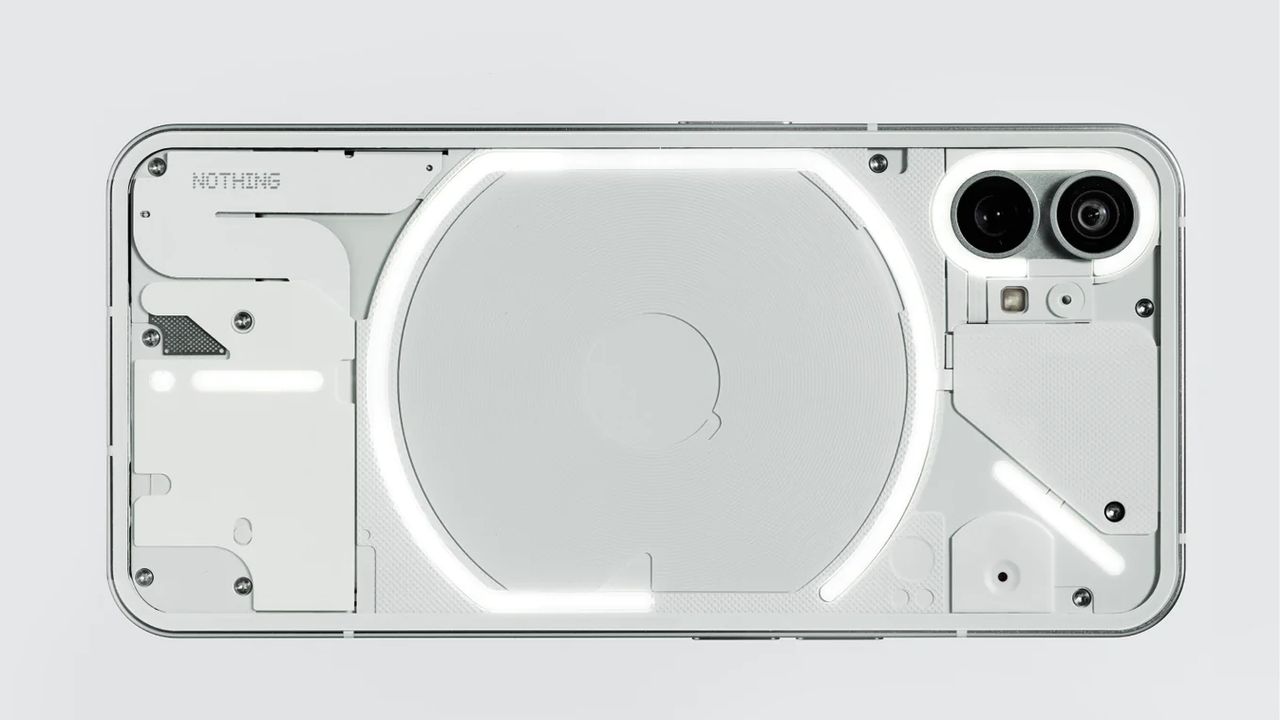
Using a Nothing CMF Phone 1, the Donjon bypassed the Android operating system completely, recovered the PIN, decrypted storage, and extracted seed phrases from multiple crypto wallets.
The flaw affects devices using Trustonic’s Trusted Execution Environment alongside MediaTek processors, found in roughly one in four Android smartphones worldwide.
Article continues below
Attackers can connect a powered-down phone through USB and retrieve root cryptographic keys before the operating system loads.
Once obtained, these keys allow offline decryption of storage and brute-forcing of the device PIN, exposing application data, including messages, photos, and wallet information.
Zero-click attacks reveal that Android smartphones frequently lack sufficient hardware and firmware protections to secure sensitive user information against advanced exploits.
“This research proves what we’ve long warned: smartphones were never designed to be vaults. While this can be patched, and we encourage all users to update with the latest security fixes,” said Charles Guillemet, Chief Technology Officer of Ledger.
“If your crypto sits on a phone, it’s only as safe as the weakest link in that phone’s hardware, firmware, or software.”
The Donjon team conducts regular audits of Ledger’s devices and third-party hardware, responsibly disclosing vulnerabilities to allow manufacturers to issue fixes before exploitation occurs.
Ledger disclosed this vulnerability to MediaTek and Trustonic under the standard 90-day disclosure process, providing time for security patches to reach affected OEMs.
MediaTek confirmed it delivered updates to OEMs on January 5, 2026, and the vulnerability was publicly disclosed on March 2, 2026, as CVE-2025-20435.
Users should immediately install security updates to mitigate potential attacks, as firmware capable of being upgraded remains critical for patching zero-day exploits effectively.
This exploit reveals the risks inherent in relying on mobile devices to store private data, including crypto wallets and other sensitive information.
All data stored on Android smartphones remains susceptible to hardware-based attacks, emphasizing that immediate patching is the only practical defense against advanced threats.
Users should be aware that even modern business smartphones carry inherent security risks, and hardware, firmware, or software flaws can expose sensitive data without warning.
Sensitive business or personal data should not be considered secure on mobile phones, and reliance on these devices alone for storing assets is inherently risky.
Follow TechRadar on Google News and add us as a preferred source to get our expert news, reviews, and opinion in your feeds. Make sure to click the Follow button!
And of course you can also follow TechRadar on TikTok for news, reviews, unboxings in video form, and get regular updates from us on WhatsApp too.